- Main
- Business & Economics - Management & Leadership
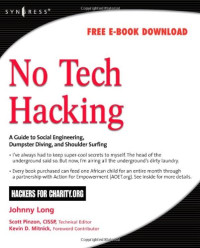
- No Tech Hacking: A Guide To Social...

No Tech Hacking: A Guide To Social Engineering, Dumpster Diving, and Shoulder Surfing
Johnny Long, Jack Wiles, Scott Pinzon, Kevin D. Mitnick你有多喜歡這本書?
文件的質量如何?
下載本書進行質量評估
下載文件的質量如何?
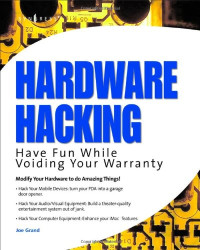
As the cliché reminds us, information is power. In this age of computer systems and technology, an increasing majority of the world's information is stored electronically. It makes sense then that as an industry we rely on high-tech electronic protection systems to guard that information. As a professional hacker, I get paid to uncover weaknesses in those systems and exploit them. Whether breaking into buildings or slipping past industrial-grade firewalls, my goal has always been the same: extract the informational secrets using any means necessary. After hundreds of jobs, I discovered the secret to bypassing every conceivable high-tech security system. This book reveals those secrets, and as the title suggests, it has nothing to do with high technology. As it turns out, the secret isn't much of a secret at all. Hackers have known about these techniques for years. Presented in a light, accessible style, you'll get to ride shotgun with the authors on successful real-world break-ins as they share photos, videos and stories that prove how vulnerable the high-tech world is to no-tech attacks.
As you browse this book, you'll hear old familiar terms like "dumpster diving", "social engineering", and "shoulder surfing". Some of these terms have drifted into obscurity to the point of becoming industry folklore; the tactics of the pre-dawn information age. But make no mistake; these and other old-school tactics work with amazing effectiveness today. In fact, there's a very good chance that someone in your organization will fall victim to one or more of these attacks this year. Will they be ready?
As you browse this book, you'll hear old familiar terms like "dumpster diving", "social engineering", and "shoulder surfing". Some of these terms have drifted into obscurity to the point of becoming industry folklore; the tactics of the pre-dawn information age. But make no mistake; these and other old-school tactics work with amazing effectiveness today. In fact, there's a very good chance that someone in your organization will fall victim to one or more of these attacks this year. Will they be ready?
年:
2008
出版商:
Syngress
語言:
english
頁數:
309
ISBN 10:
1597492159
ISBN 13:
9781597492157
文件:
PDF, 21.50 MB
你的標籤:
IPFS:
CID , CID Blake2b
english, 2008
該文件將發送到您的電子郵件地址。 您最多可能需要 1-5 分鐘收到它。
該文件將通過電報信使發送給您。 您最多可能需要 1-5 分鐘收到它。
注意:確保您已將您的帳戶鏈接到 Z-Library Telegram 機器人。
該文件將發送到您的 Kindle 帳戶。 您最多可能需要 1-5 分鐘就能收到它。
請注意:您需要驗證要發送到 Kindle 的每本書。 檢查您的郵箱是否有來自 Amazon Kindle 的驗證郵件。
轉換進行中
轉換為 失敗
最常見的術語
相關書單

























































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  轉換文件
轉換文件 更多的搜索結果
更多的搜索結果 其他特權
其他特權